Field Report: Adaptive Phishing Mitigation & Layered Defense in High-Stakes Environments
Author: IT Cyber Works
Focus Areas: Email Security, Tenant Hardening, User Experience Optimization
Subject Environment: High-Volume Legal Practice
1. The Threat Landscape
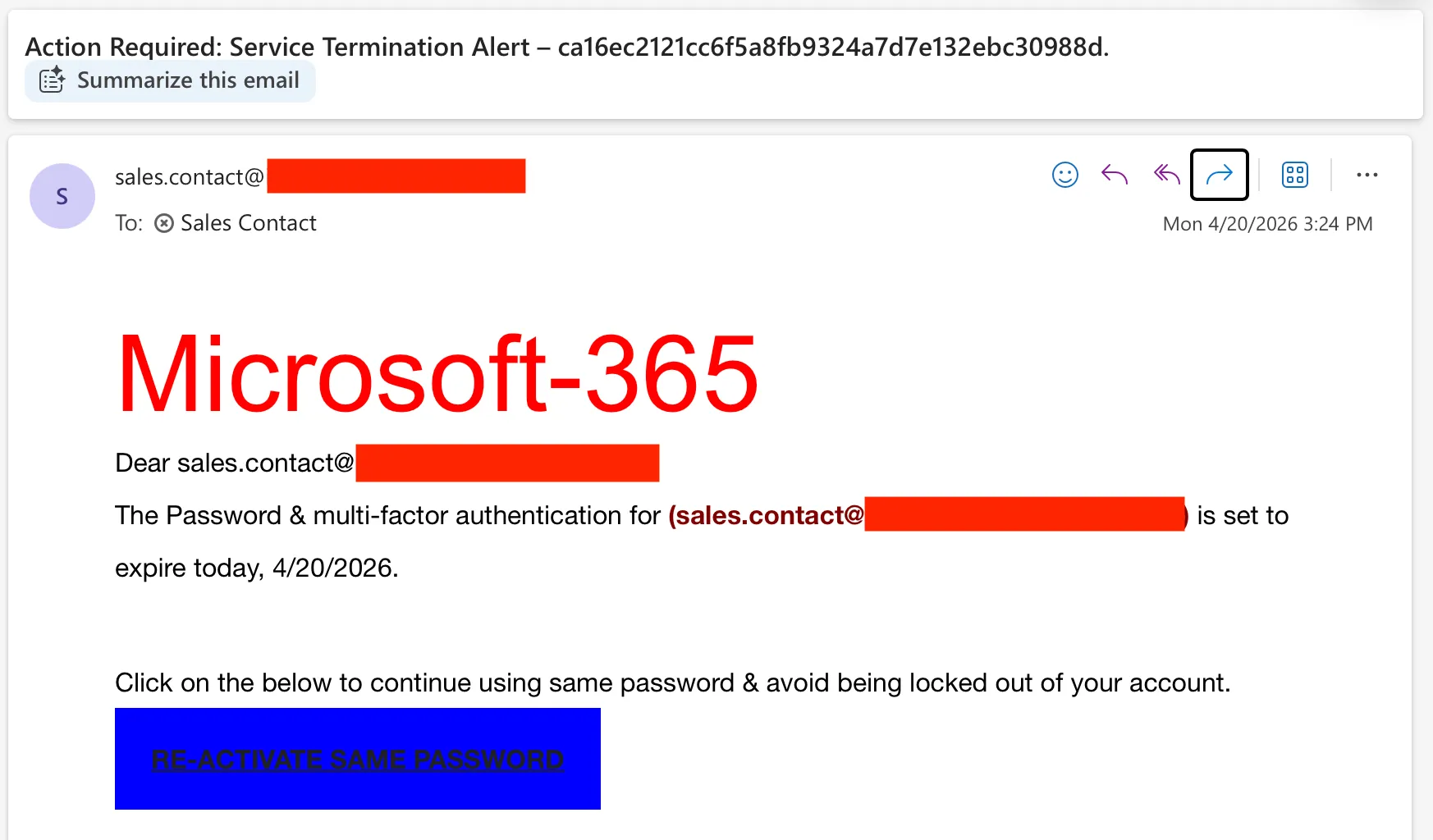
A sophisticated, highly targeted phishing campaign penetrated the initial perimeter of a prominent regional law firm. Utilizing an “Action Required: Service Termination” pretext, the malicious payload was meticulously crafted to harvest administrative and user credentials for their Microsoft 365 tenant. Though the email accurately spoofed a trusted internal address, it originated from unauthorized external infrastructure. In legal and clinical environments where strict data confidentiality is federally mandated, compromised credentials represent an immediate, existential threat to the organization.
2. Technical Diagnostic Deep-Dive
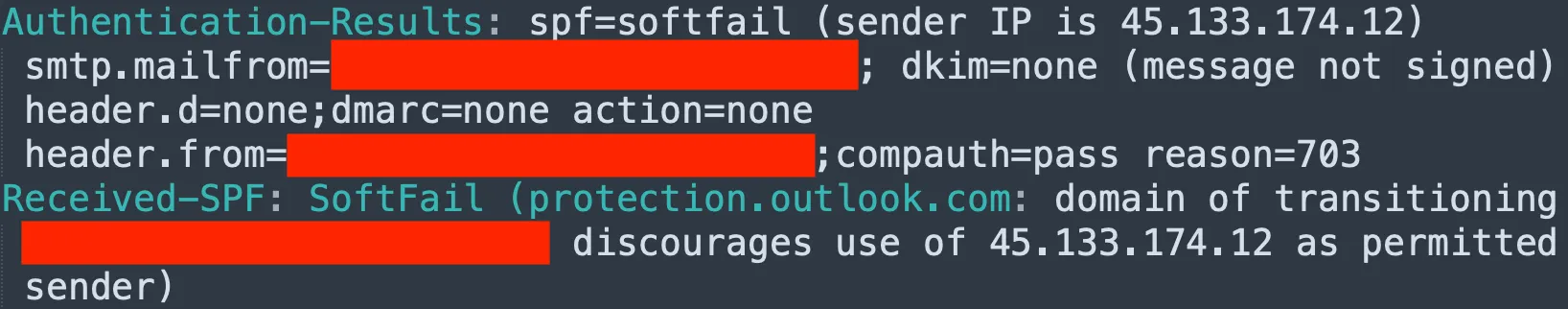
A forensic analysis of the raw email headers exposed two critical failures during transit that standard, unconfigured filtration layers completely bypassed:
- Authentication Failure: The origin IP address (
45.133.174.12) lacked authorization in the sender domain’s DNS records, resulting in a verifiablespf=softfail. - Integrity Gap: The payload lacked a valid DKIM cryptographic signature, confirming the message was forged and its transit integrity severely compromised.
3. Multi-Layered Remediation Architecture
To neutralize the active threat and fortify the firm against future campaigns—without impeding the high-speed workflow required by attorneys and clinical staff—we engineered and deployed a three-tier defense-in-depth architecture:
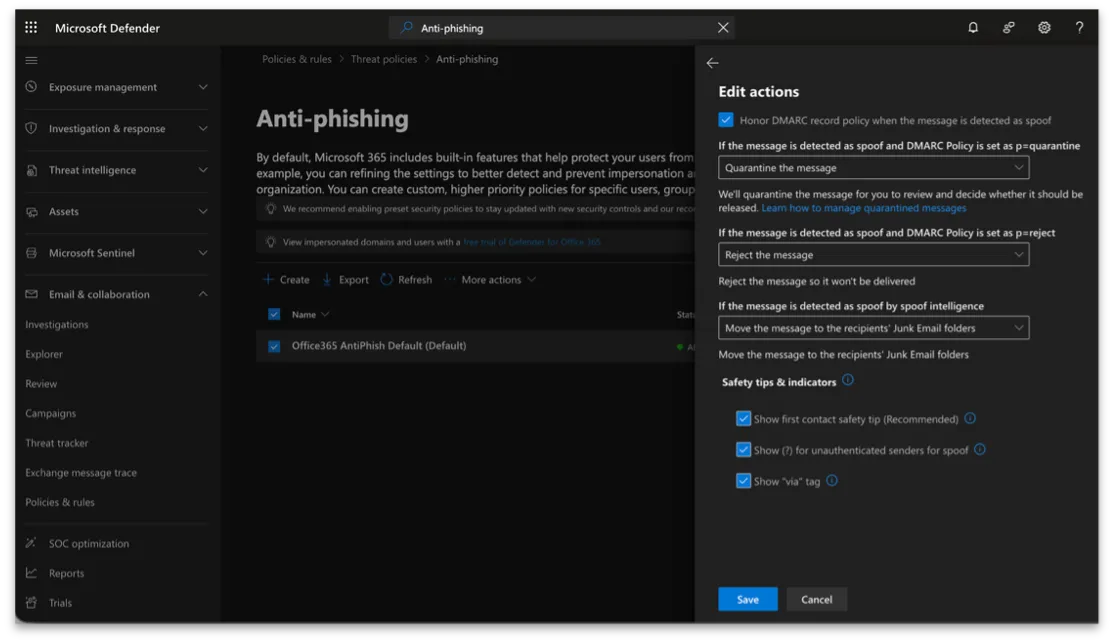
Layer 1: Global Policy Hardening (Microsoft Defender)
- Aggressive Quarantine: Re-engineered the default Anti-phishing policy to execute forced quarantines on spoofed messages, terminating their delivery rather than passively routing them to a Junk folder where they could still be interacted with.
- Visual Safety Nets: Activated First Contact Safety Tips and injected Unauthenticated Sender
(?)indicators natively into the Outlook client to serve as immediate visual threat cues.
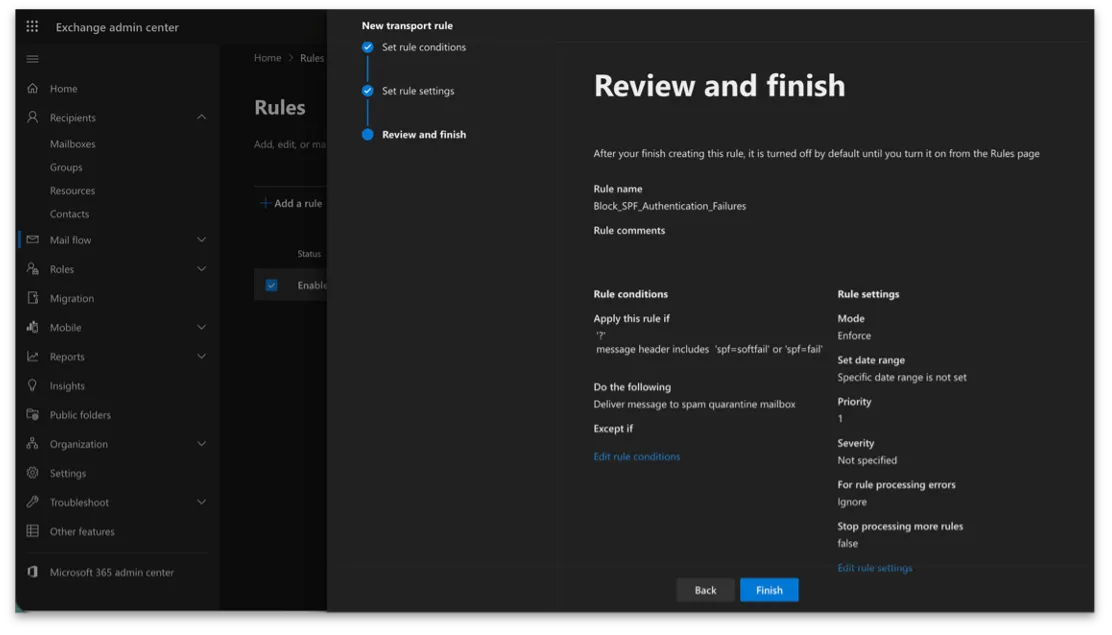
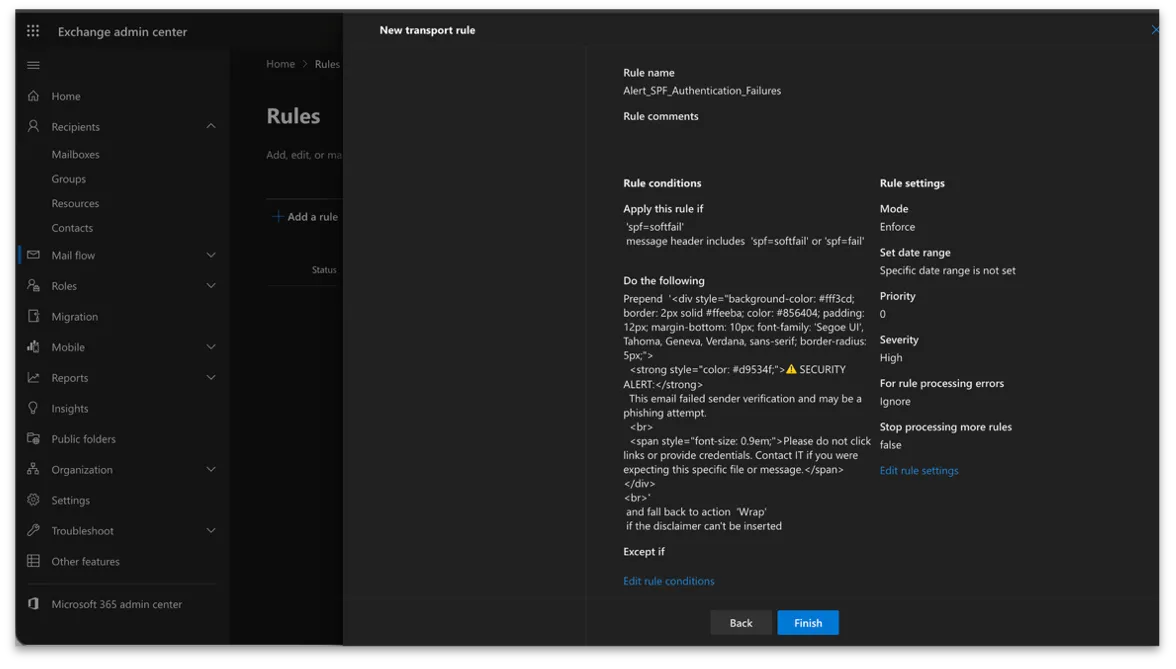
Layer 2: Conditional Mail Flow Logic (Exchange Admin Center)
- Authentication-Based Routing: Authored a precision Exchange Transport Rule (ETR) programmed to inspect the
Authentication-Resultsheader algorithmically. - Strict Triggering: The automation only triggers when
spf=softfailorspf=failflags are detected, guaranteeing that legitimate correspondence flows transparently without processing delays.
Layer 3: Adaptive User Education (Dynamic Alerts)
Conventional security banners placed on all external emails rapidly lead to psychological “banner fatigue,” causing users to unknowingly ignore real threats. We replaced their static warnings with Conditional HTML Disclaimers.
- The Result: The system now prepends a high-visibility, aggressive warning banner (⚠️ SECURITY ALERT) exclusively to messages that fail deep authentication checks. By restricting alerts to verified technical risks, the firm’s staff now treats the warnings with appropriate, immediate caution.
4. Business Impact
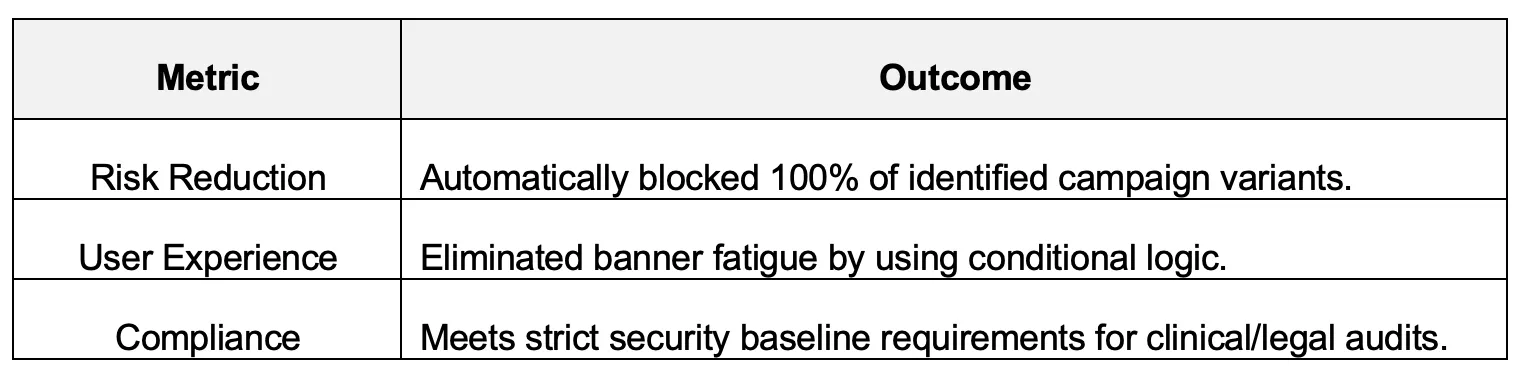
Conclusion
This incident illustrates that superior cybersecurity in high-stakes environments extends far beyond simply purchasing standard tools; it demands precision engineering and clinical configuration. By fusing global Microsoft Defender policies with custom automated logic and adaptive psychological alerts, we neutralized an active exploit and established a hardened, resilient blueprint for the client’s ecosystem.
For practices processing highly sensitive health or legal data, this proactive, layered approach is entirely non-negotiable. It proves that ironclad security measures can arrest modern threats transparently, maintaining unparalleled operational integrity and upholding absolute client trust.